This blog is a great read for those who want to understand the finest JavaScript dependency injection practices. The following are the main highlights of this blog:
- Defining dependency injection
- Best JavaScript dependency injection practices
- Risks associated with front-end JavaScript dependency injection
- Conclusion
Defining Dependency Injection
Dependency injection is widely recognized as a software design pattern. In this, a function or object uses other functions (dependencies) or objects without considering their implementation-related details. The aim of giving dependencies to objects where they are required is the injector’s responsibility. This injector is often referred to as a container, provider, or an assembler. These are widely used by web development company and custom WordPress development company.
Take into account how gaming consoles require a cartridge or compatible disc to operate. Different cartridges or discs feature game-related information. Here, if you are a gamer, then you do not require any knowledge about a console’s internals. The gamer just needs to put the cartridge or game disc in to play the desired game. Similarly, writing code or creating software this way makes it rather effortless to replace or remove components, decrease boilerplate code, and write unit tests in a codebase.
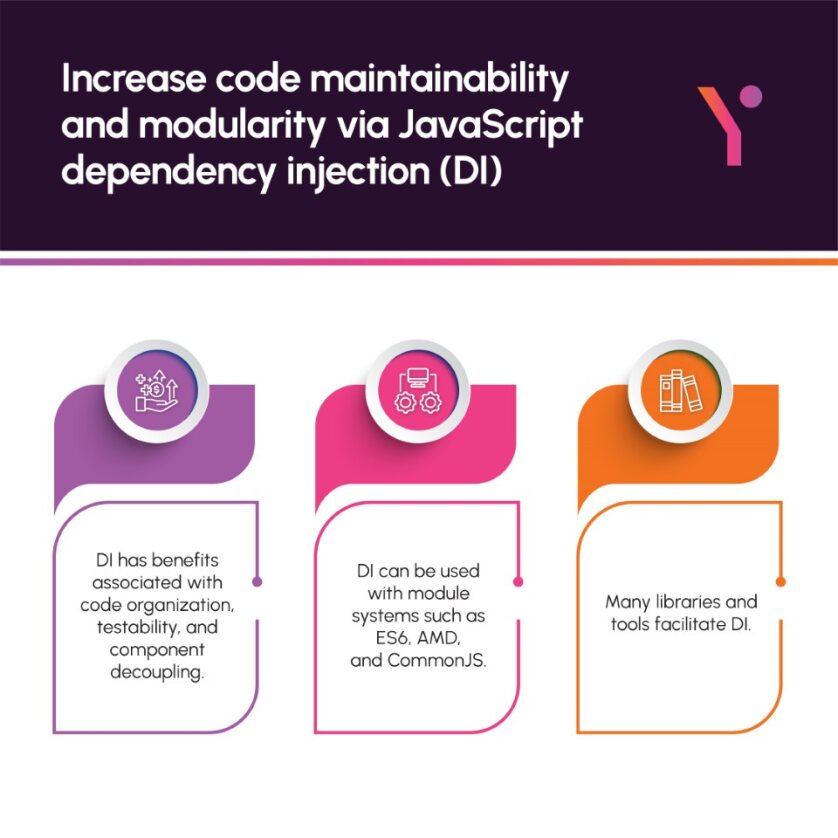
Commonly, dependency injection is implemented in several languages, such as Python and Java. However, you may not commonly see a JavaScript dependency injection. Still, this does not mean that this decreases the importance of the JavaScript dependency injection.
The following are some of the best practices for JavaScript dependency Injection:
Best Practices for JavaScript Dependency Injection
Regular Scanning – You need to regularly scan client-side code. This is done to identify unauthorized scripts and anomalies. This scanning will assist you in coming across a malicious code. The scanners have the option of making use of a host of automated scanning tools, as these will greatly ease the overall detection process.
Security Linter:
This tool is also referred to as a basic static code analyzer. It identifies a code’s errors and will also identify prospects that would evolve into any sort of security vulnerability.
Software development best practices :
These should be followed whenever working with JavaScript. Another thing that must be done besides following software development best practices is to perform regular code testing. The result here will be that you will make sure that a code is free from errors and consists of a lesser number of vulnerabilities.
Utilizing Content Security Policies (CSPs):
These will offer an additional layer of safety against code injection attacks. This is done by permitting a web page to state a particular amount of trusted content sources. This includes stylesheets, scripts, and other different resources. An important property of CSPs is that they can put restrictions on content types that a browser can both load and execute. The outcome here is that they effectively limit an attacker’s ability to run malicious code present on a given web page.
Keeping JavaScript Libraries:
You should make sure that your JavaScript libraries are up to date. This can be done by regularly testing, patching, and updating them. Another thing that you must do is to watch out for blacklisted libraries.
Carefully selecting the frameworks and libraries:
When you are about to select a library or framework, go for the option that better takes care of your overall security concerns. At the same time, it should not feature known vulnerabilities. There are many reputed libraries and frameworks, such as React, Vue.js, and Angular, that have robust built-in security features.
Implementation of access control:
This will go on to declare which users can access which code portions. The result here will be that attackers won’t be able to execute code in an application.
Validating user inputs:
A very fine practice is to validate user inputs from the server and the client side. This will then pave the way for additional security. This sort of validation also means that data entered by a user is according to the required format and it isn’t malicious in its nature. For instance, you may utilize a JavaScript function to see if a person’s username features just alphanumeric values and is free from codes that can cause vulnerabilities in an application.
Web security awareness:
Organizations should run web security awareness programs for their workforce. This will help the employees be more vigilant regarding today’s cyberattack trends.
Risks related to Front-End JavaScript Dependency Injection
It is well-understood that JavaScript dependency injection is useful for an application. However, dependency injection can raise its attack surface. This means that it becomes feasible for hackers to fool the application into pulling malicious scripts from a number of external repositories and then initiate attacks that are according to such scripts.
Let’s consider that an attacker makes a malicious script and then publishes the script with the same file name in the public repository, but this has a greater version number. In this scenario, there is a high degree of chance that the installer will go on to pull that script and not the real one. Another point is that attackers can use these scripts to launch an offensive at a site in many ways.
The below mentioned are some of the most renowned JavaScript dependency injection framework vulnerabilities:
Website Spoofing:
This is a brand impersonation attack in which a hacker goes on to make fake identical emails, web pages, or social media accounts. The purpose here is to fool users so that they engage with them. The users would be under the impression that they are interacting with a trusted brand. The hackers pretend to be a true brand and depend upon social engineering to get user payments and/or input data. Here, users are not aware of the overall malicious activity taking place.
Cross-Site Request Forgery:
This is where hackers fool users so that the latter takes some action. Additionally, hackers may use stolen credentials and showcase themselves as authorized users. This allows the hackers to do actions that are done without a user’s consent.
Cross-site scripting:
Here, someone with malicious intent puts in malicious client-side code. This allows the attacker to steal a user’s input data.
Concluding Remarks
There is little denying the fact that JavaScript dependency injection offers a great number of benefits. This includes improving code reusability and modularity. But it must also be understood that this can make an application become somewhat vulnerable to cyberattacks. If you want to avoid the negative effects of JavaScript dependency injection, then you need to follow the best practices stated in this blog. On top of this, you should also remember that the stated best practices are not 100% guaranteed to give you the desired results.
Finally, understand that Futurbyte is a well-renowned software solutions provider that is known for its JavaScript-based solutions. We will help you with your projects ranging from custom web development service and webapp development.
Frequently Asked Questions
Sure, dependency action is a well-recognized software design pattern. In this pattern, a function or an object utilizes other functions (dependencies) or objects, and this is done without giving any sort of concern to their implementation details.
This is how you inject dependencies in Java –First, you need to identify dependencies.Second, inject dependencies.In the second step, there are a host of ways you can inject dependencies in a class. For instance, you can pass them as arguments in a class’s constructor. Also, it must be understood that dependency injection will go on to enhance the testability and design of a codebase. This ultimately makes it become a valuable approach throughout the software development phase.
Understand that a dependency injection (DI) container is often called an inversion of control (IoC) container. This framework assists with dependency injection. It goes on to automatically create and inject dependencies for us.
When you go on to register services in a container, you are required to set the lifetime that you need to utilize. Here, after a result object has been made by the container, the service lifetime will go on to control how long it will exist.Commonly, three lifetimes are utilized with Microsoft Dependency Injection Container. These are:TransientScopedSingleton
Sure, these are some prominent advantages of using dependency injection:It lets your code become more loosely coupled. This happens because classes are void of any hard-coded dependencies.It eases (or makes it possible) isolation in unit testing. It is important to note here that without dependency injection, it is very hard to isolate components in unit testing.If facilitates a good design, like the single responsibility principle.It enables switching to quickly replace implementations/dependencies.
Have questions or feedback?
Get in touch with us and we‘l get back to you and help as soon as we can!